Accredited InvestorsAltcoinAnatoli UnitskyAnti-Money Laundering (AML) In CryptoAPIArbitrageArtCoin TokenArticle DirectoryASICAuction Terminology GlossaryBasics of Stock Market InvestingBear MarketBest Crypto Payment Provider In the WorldBitcoinBlockchainBlockchain ConfirmationBlockchain Consensus MechanismBlockchain ForkBlockchain GlossaryBored Ape Yacht ClubBuild a Business That OutperformsBull MarketBuying SkyWay SharesByzantine Fault Tolerance (BFT) ExplainedCasascius CoinCentral Bank Digital Currency (CBDC)Centralized Crypto ExchangeCoinCoinsetCold WalletCollateralCommodity Futures Trading Commission (CFTC)Cross-Chain TechnologyCRUCrypto ExchangeCrypto GlossaryCrypto JokesCrypto Terms to KnowCrypto TickerCryptocurrencyCryptographyCryptojackingCryptounit BlockchainCryptounit GlossaryCryptounit ProgramdApp (Decentralized Application)Dead CoinDecentralized Exchange (DEX)Decentralized Finance (DeFi)Difference Between Bitcoin and EthereumDifferent Ways of Investing MoneyDigital CurrencyDistributed LedgerDo Your Own Research (DYOR)Dollar Cost Averaging (DCA)Dow Jones Industrial Average (DJIA)EncryptionERC-20ERC-721EthereumEvoScentFear Of Missing Out (FOMO)Fear, Uncertainty and Doubt (FUD)Fiat MoneyFNT Fintech CompanyGenesis BlockGlobal Unit PayGlossary of Banking TermsGlossary of Business TermsGlossary of Financial TermsHalvingHODLHot WalletHow Do I Start InvestingHow Rich is Satoshi Nakamoto?How to Create a BlockchainHow to Find Private InvestorsHow to Get Into FintechHow to Program Smart ContractsI Am Thrilled to Be a Part of This Global ProjectInitial Coin Offering (ICO)Initial Public Offering (IPO)Initial Token Offering (ITO)Innovation Basalt TechnologyInnovative Transportation TechnologiesInternational Bank Account Number (IBAN)Investing in Gold Mining StocksInvesting in Gold MiningJagerJoy of Missing Out (JOMO)Know Your Customer (KYC)LedgerLiquidity in CryptocurrencyMaker and Taker Fees in Crypto TradingMarket Capitalization (Market Cap)Meme CoinMetal Credit CardMetaMaskMillenials Now Have Access to Generational WealthMy Best Investment EverNew Digital EvolutionNFT GlossaryOff-Chain TransactionsOn-Chain TransactionsOpen Edition NFTPeer-to-Peer (P2P)Personal Loan GlossaryProbably the Best STO on the MarketProof of Stake (PoS)Real Estate Glossary of TermsReal Estate Investing GlossaryRebase TokenSecurities and Exchange Commission (SEC)Security Token ExchangesSecurity Token Offering (STO)Soulbound Decentralized Identities for Security TokensSoulbound ID Launch by Stobox Proves a SuccessSoulbound TokensStoboxStock Market GlossaryTestimonialsTether Platform and Token (USDT)UnitEx ExchangeUnitsky String TechnologiesUNTBUSDUValidatorWe Started Investing When We Were 25What are Blue Chip NFT?What are Blue Chip Stocks?What are Crypto Assets?What are Crypto Smart Contracts?What are CryptoPunks NFT?What are Digital Assets?What are Digital Collectibles?What are Gas Fees?What are Gas Wars?What are Hashmasks?What are Non Fungible Tokens?What are Non-Sufficient Funds (NSF)?What are Soulbound Tokens (SBT)?What are Stablecoins in Crypto?What are Transactions Per Second (TPS)?What are Utility NFTs?What are Utility Tokens?What Does Burning Crypto Mean?What Does Diamond Hands Mean?What Does Paper Hands Mean?What Does To The Moon Mean?What Does WAGMI Mean?What Happened to Satoshi Nakamoto?What is a 51% Attack?What is a Baby Boomer?What is a Backlink?What is a Banner?What is a Barcode?What is a Bid-Ask Spread in Crypto?What is a Block in Blockchain?What is a Block Reward?What is a Blockchain Address?What is a Blockchain Node?What is a Blockchain Oracle?What is a Blog?What is a Bond?What is a Bot?What is a Broker?What is a Business Accelerator?What is a Cash Cow?What is a Commercial Bank?What is a Commodity?What is a Con?What is a Credit?What is a Credit Limit?What is a Credit Rating?What is a Crypto Airdrop?What is a Crypto Bridge?What is a Crypto Scam?What is a Crypto Token?What is a Crypto Wallet?What is a Crypto Whale?What is a Crypto Winter?What is a Cryptocurrency Public Ledger?What is a Cryptocurrency Roadmap?What is a DAO?What is a Dark Pool?What is a Day Trader?What is a Dead Cat Bounce?What is a Default?What is a Derivative?What is a Digital Credit Card?What is a Fiscal Quarter?What is a Fungible Token?What is a Governance Token?What is a Grace Period?What is a Hard Fork?What is a Hot Wallet?What is a Hybrid Blockchain?What is a Hybrid PoW/PoS?What is a Joint Account?What is a Market Cap?What is a Merkle Tree in Blockchain?What is a Mining Farm?What is a Nonce? What is a PFP NFT?What is a POS System?What is a Prepaid Card?What is a Private Blockchain?What is a Private Key?What is a Public Blockchain?What is a Public Key?What is a Reserve Currency?What is a Ring Signature?What is a Routing Number?What is a Rug Pull in Crypto?What is a Safe Deposit Box?What is a Satoshi?What is a Security Token?What is a Seed Phrase?What is a Shitcoin?What is a Sidechain?What is a Soft Fork?What is a Spot Market?What is a State Bank?What is a SWIFT Code?What is a Tax Identification Number (TIN)?What is a Time Deposit?What is a Transaction Account?What is a Variable Interest Rate?What is a Virtual Assistant (VA)?What is a Virtual Card?What is a Virtual Currency?What is a Visa Card?What is a Whitelist in Crypto?What is a Whitepaper?What is Accounts Payable (AP)?What is AMA in Crypto?What is Amortization?What is an Accrual?What is an ACH Transfer?What is an Actuary?What is an Addendum?What is an Algorithm?What is an Angel Investor?What is an Annuity?What is an Asset?What is an ATM?What is an Atomic Swap?What is an Audit?What is an Avatar?What is an EIN?What is an Embargo?What is an Entrepreneur?What is an IDO (Initial Dex Offering)?What is an Interest Rate?What is an Internet cookie?What is an Investment Bank?What is an NFT Drop?What is an NFT Floor Price?What is an Ommer Block?What is an Orphan Block?What is an Outstanding Check?What is an Overdraft?What is Artificial Intelligence (AI)?What is B2B (Business-to-Business)?What is B2G (Business-to-Government)?What is Bartering?What is Bitcoin Dominance?What is Bitcoin Pizza Day?What is Blockchain Immutability?What is Blockchain Used For?What is BRICS?What is Business-to-Consumer (B2C)?What is C2C (Customer to Customer)?What is Capitalism?What is Catfishing?What is CFD Trading?What is Check Kiting?What is Cloud Mining?What is Communism?What is Content Marketing?What is Decentralization in Blockchain?What is DeFi in Crypto?What is Delisting?What is Depreciation?What is Digital Marketing?What is Diversification?What is Double Spending?What is Dumb Money?What is Dumping?What is Earnings Per Share (EPS)?What is Economics?What is Email Marketing?What is Equity?What is Etherscan?What is Fintech?What is Foreign currency?What is Forex?What is Fundamental Analysis (FA)?What is GameFi?What is Generative Art NFT?What is Gwei?What is Hard Currency?What is Hash Rate?What is Hashing in Blockchain?What is Inflation?What is Initial Game Offering (IGO)?What is Interest?What is Interest Income?What is Mainnet?What is Mastercard?What is Metaverse in Crypto?What is Mining in Cryptocurrency?What is Minting NFT?What is Mobile Banking?What is Money Laundering?What is NFT Alpha?What is NFT Metadata?What is NFT Rarity?What is NGMI Meaning?What is Nominal Interest Rate?What is Online Banking?What is Open-End Credit?What is OpenSea NFT Marketplace?What is Personal Identification Number (PIN)?What is Play-to-Earn?What is Polygon?What is Proof of Authority (PoA)?What is Proof of Work (PoW)?What is Public Key Cryptography?What is Pump and Dump?What is Quantum Computing?What is Refinancing?What is Retail Banking?What is Ripple?What is Sharding?What is Slippage in Crypto?What is Smart Money?What is Solvency?What is Soulbound ID?What is SSL?What is Staking in Cryptocurrency?What is Technical Analysis (TA)?What is Testnet?What is the Ask Price?What is the Better Business Bureau (BBB)?What is the Bid Price?What is the Dark Web?What is the InterPlanetary File System (IPFS)?What is the Gold Standard?What is the Lightning Network?What is the Prime Rate?What is the Sandbox?What is the Secondary Market?What is the World Bank?What is Tier 1 Capital?What is Tokenomics?What is TRC-20?What is Universal Banking?What is Unspent Transaction Output (UTXO)?What is Usury?What is Volatility in Crypto?What is Wash Trading?What is Web3?What is Whisper?What is XRP?What is Zero-Knowledge Proof (ZKP)?Who is Beeple?Who is Satoshi Nakamoto?Who is Vitalik Buterin?Why Tokenization is a Safe HavenWhy You Should Try Your Hand at Trading
What is Quantum Computing?
- Home
- Crypto Glossary
- What is Quantum Computing?
Quantum computing is a buzzword that is making its way into the mainstream conversation, but what exactly is it? This cutting-edge technology promises to revolutionize the way we solve complex problems and process vast amounts of data.
With its potential to revolutionize fields such as cryptography, blockchain, and cryptocurrencies, quantum computing is poised to have a significant impact on the way we store and exchange information in the digital world.
But before we dive into its capabilities and potential applications, let's explore the basic principles and underlying theories that make quantum computing a game-changer in the world of computing.
What is Quantum Computing?
Quantum computing is a fast-growing technology that uses the principles of quantum mechanics to tackle problems beyond the capabilities of traditional computers.
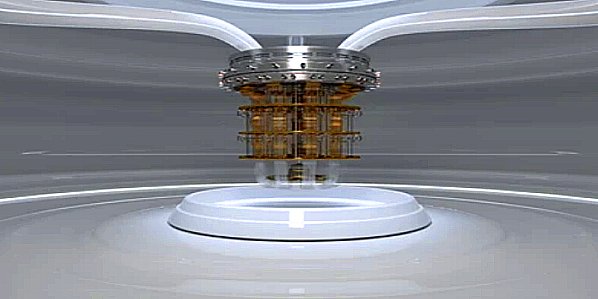
Computer engineers are constantly improving superconducting quantum processors and advancing software and quantum-classical orchestration to achieve the speed and capacity needed to revolutionize the world.
It's important to note that quantum computers are vastly different from the classic computers that have existed for over 50 years. Here's a basic overview of this groundbreaking technology.
The term "computer" may be misleading, as quantum computers operate on a different principle than classical computers.
Classical computers process data using binary bits (0s and 1s), while quantum computers use the principles of quantum mechanics. The binary bit is the basic unit of information for classical computers, while the quantum bit (qubit) is the basic unit of information for quantum computers.
Unlike classical computers, which can only store information as 0s or 1s, quantum computers can store information in superpositions, meaning they can be both 0 and 1 at the same time. To put it simply, a classical bit can store one piece of data, but a quantum qubit can hold two bits worth of data simultaneously.
Does Quantum Computing Pose a Threat to Cryptography?
Quantum computing and cryptography are intertwined in a complicated relationship. Public key cryptography, also known as asymmetric encryption, uses cryptographic protocols based on algorithms to encrypt data. It requires two separate keys, a private and a public one. The security of asymmetric cryptography relies on a mathematical principle called a "one-way function." This principle states that the public key can be derived from the private key, but not vice versa.
In 1994, mathematician Peter Shor published a quantum algorithm that could compromise the security of the most widely used asymmetric cryptography algorithms. This was a turning point in the battle between quantum computing and blockchain technology. If a potent enough quantum computer existed, it could perform decryption without knowledge of the private key and put public key cryptography systems at risk.
Quantum computing poses a threat to today's cryptography, endangering internet security protocols and privacy. Quantum computers can process data differently than classical computers, and their ability to exist in both 0 and 1 states at the same time means they can perform calculations faster.
Although currently, quantum computers cannot break any common encryption methods, technical advances are needed before they can compromise strong codes in use around the internet. The threat is theoretical for now, but it's important to prepare for a potential, yet highly improbable, war between quantum and blockchain technologies.
Quantum Computing and Blockchain: The Future of Secure Technology
The combination of quantum computing and blockchain has the potential to bring about significant change in the way we store and exchange data. If cryptography advances to create increasingly quantum-resistant encryption methods, or if quantum encryption is integrated into blockchains, the marriage of these promising technologies could aid in the creation of a more secure, democratized internet.
Using quantum keys in conjunction with a blockchain network could help protect against attacks from both classical and quantum computers. This would provide a more secure platform for storing and exchanging data, and it would bring about a new era of secure communication.
Future research into post-quantum cryptography will play a critical role in enabling the development of robust blockchain applications. As quantum computing advances, it will become increasingly important to find new ways to protect data from quantum-based attacks. By combining the strengths of quantum computing and blockchain, we can create a more secure and reliable platform for exchanging data and information.
In conclusion, the combination of quantum computing and blockchain has the potential to revolutionize the way we store and exchange data. With the right investments in research and development, this exciting technology could bring about a more secure and democratic internet, and it is sure to play a major role in shaping the future of technology.
Related Articles

Cryptography
Cryptography is the art and study of mechanisms for secure communication.

Cryptounit Blockchain
Cryptounit blockchain, based on EOSIO, is designed to enable vertical and horizontal scaling of decentralized applications linking the real economy and decentralized finance (DeFi).

Cryptocurrency
Cryptocurrency, abbreviated as crypto, refers to any digital form of money that employs cryptography to safeguard transactions such as buying, selling, transferring, and staking.

What is a Public Key?
The public key is created using asymmetric key cryptographic algorithms in public key cryptography.

What is a Private Key?
A private key, commonly known as a secret key, is a mathematical key used to generate digital signatures and, depending on the algorithm, to decrypt messages or files encrypted with...

Encryption
Encryption is a security technology that scrambles data, such as text, into a secret message that cannot be read by another person.
- Home
- Crypto Glossary
- What is Quantum Computing?